Hardware wallets are important for storing cryptocurrencies securely, but they are not immune to side-channel attacks, which exploit unintentional leaks of ...
You need to understand the potential threats posed by quantum computing to hardware wallets, as advancements in this technology may compromise the security of ...
You may not realize how vulnerable your cryptocurrency holdings are to physical threats. Ensuring the security of your hardware wallet is necessary, as a ...
Many cryptocurrency users overlook the importance of security audits for their hardware wallets, putting their investments at risk. Ensuring your ...
Just how safe are your digital assets? This post examines into the backdoor risks associated with hardware wallets, emphasizing the differences between open ...
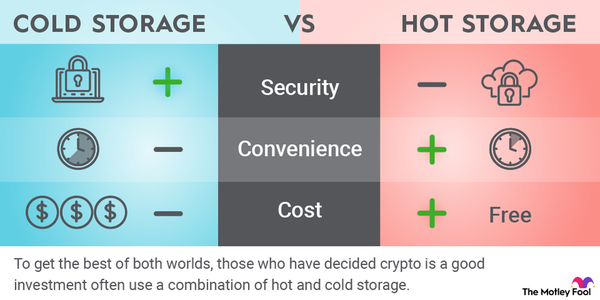
Cold storage solutions offer the highest level of security for cryptocurrency by keeping assets completely offline. Utilizing air-gap technology, these methods ...
Over the past few years, securing cryptocurrencies has become increasingly vital as threats evolve. With hardware wallets being a popular choice for storing ...
There’s a growing need for transparency in the world of cryptocurrency as vulnerabilities in hardware wallets can expose users to significant risks. ...
Security is paramount in the world of cryptocurrency, especially when it comes to cold wallets. Cold wallet stress testing serves as an necessary safeguard, ...
Encryption plays a vital role in protecting sensitive data transmitted between hardware wallets and user devices. Utilizing encrypted channel protocols ensures ...
Awareness of crypto security issues is vital for businesses in today’s digital landscape. Establishing a strong security culture not only mitigates risks ...
Wallet security is paramount in the digital age, where threats to cryptocurrency assets are ever-present. Using hardware wallets provides a significant layer ...
Over the past few years, cold storage has emerged as a highly secure method for cryptocurrency enthusiasts to safeguard their assets. However, the challenge ...
Wallet security goes beyond digital safeguards; it also involves physical protection against emerging threats like heat-based attacks. These attacks exploit ...
Most users believe their hardware wallets provide ultimate protection for their cryptocurrencies, but a breach can compromise sensitive assets. This blog post ...
You may not realize the importance of hardware wallet security in protecting your digital assets. Adhering to internationally recognized standards like ISO ...
It’s important to keep your hardware wallet secure while ensuring it remains hidden from potential thieves and prying eyes. Utilizing covert storage ...
Most hardware wallets feature a kill switch function that allows users to execute an emergency wipe of their device. This procedure is necessary to protect ...
There’s a significant psychological factor influencing how individuals choose cryptocurrency wallets: confirmation bias. This cognitive bias can lead ...
Most hardware wallets implement a secure boot process to ensure firmware integrity, protecting users from malicious attacks. This process initiates system ...